INTRODUCTION
Strengthening digital resilience is key to mitigating cyber crimes
Data breaches, ransomware events, and distributed denial of service (DDoS) attacks against critical healthcare infrastructure have become one of the most critical risk management topics today.
There has been an exponential growth of cybercrime in recent years.
- Between 2004 and 2021, 50 large data breaches resulted in the loss of 17.5 billion patient health information (PHI) records.
- In the first six months of 2022, 337 separate data loss events at healthcare organizations resulted in more than 19 billion individual records being lost.
- Since 2019, 50% of all healthcare enterprises have suffered at least one data breach event.
Criminal organizations target healthcare organizations in pursuit of lucrative payouts. While many healthcare enterprises are finally beginning to form a healthcare cybersecurity plan, such as the zero-trust framework (see infographic 1), much more needs to bed one to safeguard organizations against cybercrime.
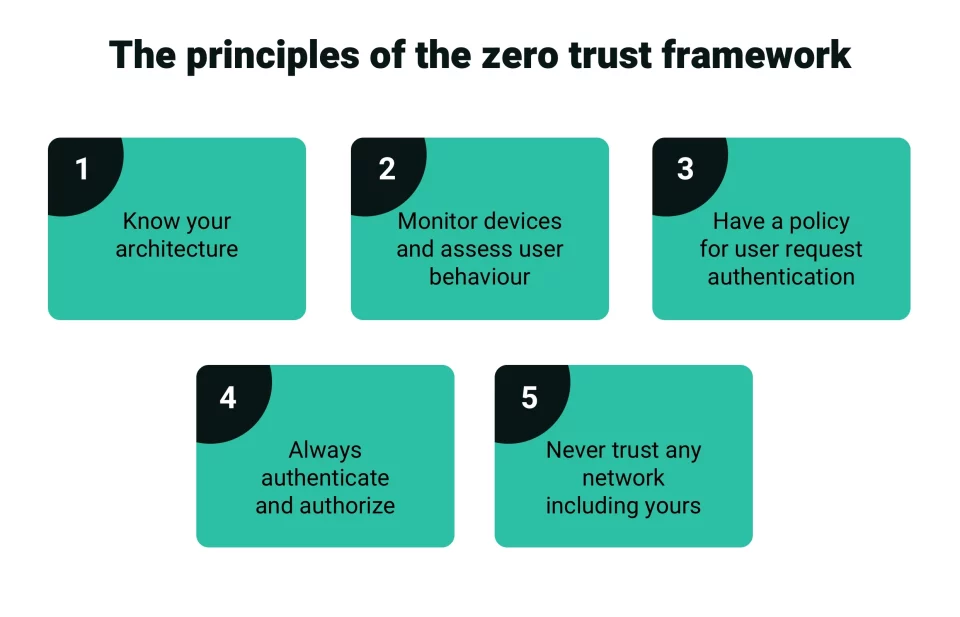 Healthcare enterprises are adopting the zero trust principles for cybersecurity
Healthcare enterprises are adopting the zero trust principles for cybersecurity
THREATS
Top cyber security threats facing healthcare enterprises in 2023
According to IBM, the average cost to respond to a healthcare data loss event in 2022 reached $10.1 million — the single highest cost associated with data breaches in any industry. Yet, as staggering as these costs can be, they pale in comparison to the damage caused to the reputation of the medical professionals and organizations connected to the most devastating breach events.
Healthcare leaders therefore have a vested interest in completing strategic investments to safeguard their organization’s data against the growing risk of cybercrime.
The impact of cyber threats has been so pervasive it has changed the insurance criteria for many businesses. Greater due diligence, recruiting senior cyber security professionals in leadership roles, and implementing a modern threat reduction strategy are a must.
First, there is a need to identify the various threats to an enterprise.
Malware
In just the first six months of 2022, there were more than 2.8 billion malware attacks recorded globally. Malware is software designed specifically to penetrate defensive systems, compromise system data, and provide attackers with lateral access that allows them to move through different elements of a digital health technology stack.
Cyber-security researchers estimate that there are 5,60,000 new pieces of malware found every single day, with more than one billion unique programs in operation around the world. Malware is malicious software and includes:
- Virus (copies itself and infects computers)
- Worm (sends copies of itself to other computers in the network)
- Spyware (collects information from computers stealthily)
- Adware (plays, displays, and downloads ads on computers)
- Trojan horse (disguised as useful, it harms computers and steals information)
Ransomware
Ransomware is the most feared cyber attack variant and is designed to take control of a victim’s access to files on their computer by encrypting them. Cyber attackers demand a ransom sum to be paid to share the decryption key, which is the only way to restore access. Ransomware attacks are destructive to an enterprise and place executive leadership teams in an extremely challenging position, as some also steal data to extort more money.
In the first week of December 2022, one of the largest healthcare organizations, and subsidiary of Columbia Health, Keralty reported being victimized by a ransomware attack launched by the Ransom House criminal organization, which resulted in the loss of 3TB of lost data.
Chaos, Dharma, Xorist, Trigona, STOP, and Medusa Locker are just a few ransomware programs with new variants attacking medical service providers in recent months.
Data breaches
Data breach attacks involve data theft or leaks without authorization or knowledge of the healthcare providers. While some attacks are executed merely as crimes of opportunity meant to deliver profits, they are frequently launched as a form of corporate espionage and warfare, too.
It is becoming extremely easy for threat actors to infect digital systems, cloud services, mobile applications, hardware devices, and other touch points that link an organization to its patients, employees, third-party contractors, and suppliers.
Data poisoning attacks
One of the newest forms of cyber exploitation involves the use of purposefully infecting artificial intelligence-powered data collection tools to compromise and falsify data at scale. Called a data poisoning attack, it is to limit the ability of artificial intelligence and machine learning systems to produce valid and reliable results.
AI/ML adoption is an important tool to streamline operations and achieve better outcomes for patients. Efforts to manipulate AI-generated data create a new challenge for cyber security.
MITIGATION
Need for increased cloud security measures
As hospital operations shift towards software-as-a-service (SaaS), there is a greater need for increased cloud security measures. Without endpoint security measures in place, every single user and program that interacts with a cloud network could be used to launch an attack. Here are some precautions to protect the cloud from data breaches:
- Educate employees on how to avoid data compromise and report suspicious activities.
- Create data security standards and update them regularly.
- Monitor the network round-the-clock remotely.
- Have a robust data backup and recovery protocol.
- Utilize the impact of blockchain technology on society
Biometrics
Cloud-based biometric solutions use a person's unique characteristics captured in a picture or template to authenticate their identity and provide them access. These new technologies—voice recognition, iris scanning, face recognition, and fingerprint storage—promise to offer an added layer to multi-factor security, which ultimately should create safer and more secure environments. As biometric security is handled by third-party providers, they should be made tamper-proof.
The Internet of Things
The numbers are staggering—as of 2019, more than 82% of healthcare organizations had experienced an IoT-based cyberattack, with 30% of those incidents directly threatening end-user safety.
By the beginning of 2022, it was reported that as many as 70% of all medical devices were still running outdated and vulnerable versions of Microsoft Windows.
To safeguard against IoT attacks, it is important to:
- Change the name of the router settings given by the manufacturer.
- Change all the default and privacy security settings of the wifi network.
- Keep your software and firmware updated.
- Choose a strong password.
- Disconnect IoT devices when not in use.
- Turn off the universal plug-and-play.
- Keep track of the latest IoT technology trends
Supply chain vulnerabilities
Modern organizations need to be responsible not only for safeguarding their system resources but being sure that their partner’s systems are up to snuff. Supply chain attacks in healthcare endanger personal, medical, institutional, and financial data. Here are the best practices toward off cyber attacks and limit the damage third-party interactions can wreak:
- Implement a zero-trust architecture.
- Plant honey tokens -fake resources posing as sensitive data.
- Secure privileged access with both external and internal defenses.
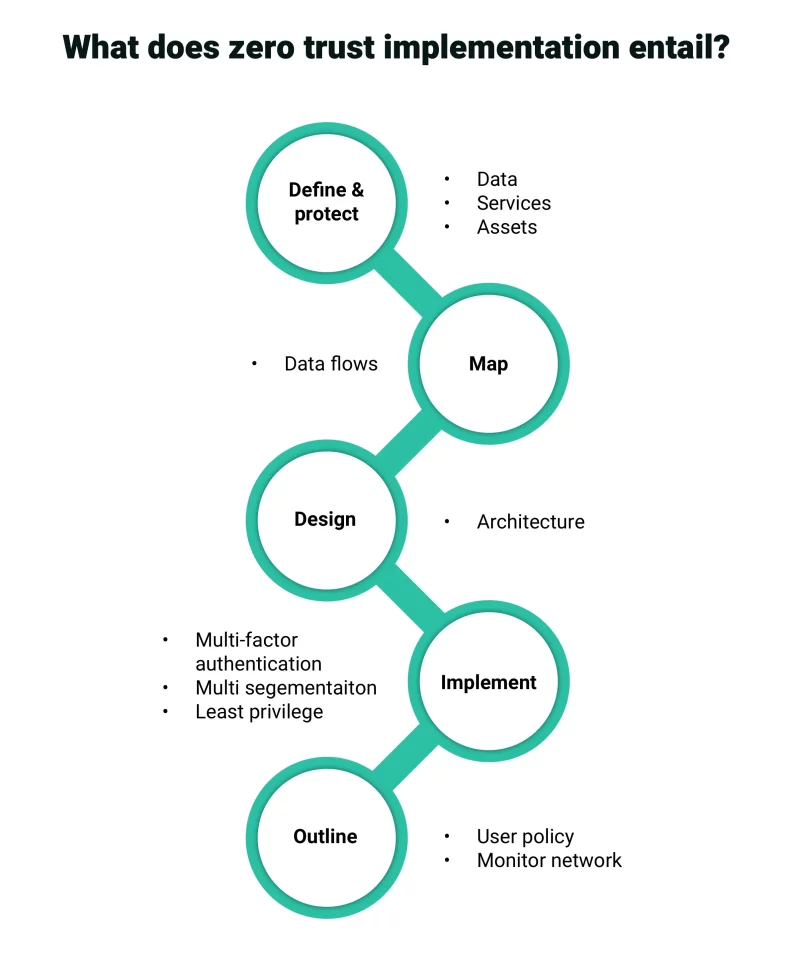 Healthcare enterprises enlist expert services to implement a zero-trust architecture
Healthcare enterprises enlist expert services to implement a zero-trust architecture
Social engineering operations
Insider threat remains one of the most significant cyber security attack vectors facing healthcare providers. All it takes is one employee to click a single link, and attackers can gain lateral access to system resources within a matter of seconds. So, enterprises should identify, prioritize, and remediate security flaws in the physical and digital health ecosystem.
The best defense is to take offensive security measures:
- Penetration testing: an authorized simulated attack performed on a computer system to evaluate its security.
- Vulnerability management: an ongoing, regular process of identifying, assessing, reporting on, managing, and remediating cyber vulnerabilities across endpoints, workloads, and systems.
- Adversary simulation: impersonating the actions of cyber attackers to get a feedback loop from the organization’s security stack and strengthen it.
Digital health ecosystems
As health providers develop digital health ecosystems across consumer and business-facing applications, cybersecurity needs to be a top-line priority. Connected health systems provide a great deal of flexibility that matches consumer expectations and demands. However, the fastest way to erase record profits is to find your healthcare organization embroiled in the latest scandal involving the loss of PHI.
To avoid theft of PHI:
- Adopt proactive security policies, including an incident readiness and response plan.
- Appoint a chief information security officer to elevate the maturity of security and draft a healthcare technology security plan.
- Integrate security into the business practice.
- Embed security features across the workflows of the organization.
CONCLUSION
Gain real-time visibility and take preventive action
Adequately addressing the persistent threat of cybercrime requires enterprise-wide ingenuity, substantial financial investment, and considered attention to ensure that vital hardware, software, technologies, devices, and critical IT infrastructure are safeguarded against malicious actors.
In today’s heightened threat environment, it is essential for enterprises to gain real-time visibility into all the activity taking place across their networks, including data paths and all touchpoints with patients, customers, suppliers, and partners.
Achieving robust digital resilience through custom software development services empowers organizations to identify, understand, and respond to cyber risks before they exceed corporate risk management criteria.